While digital technology has opened new lines of attack for scammers, they’ve also empowered us to defend ourselves from those same attacks. Thanks to proactive improvements to our operating systems and industry protocols, there are plenty of ways to keep your business safe from cyberhacks and viruses.
However, hackers don’t need to find cybersecurity flaws if they can exploit flaws in human judgment first. Using social engineering, hackers can open the door to your company’s finances, data, and employee information. Thankfully, you can follow some simple protocols to fortify your business against these attacks.
What you need to know
- Social engineering refers to hacking strategies in which the fraudsters tries to exploit human error to gain access to sensitive information.
- Hackers may use a combination of social engineering strategies and malicious code, spyware, or AI tools to access your account(s).
- You can implement security protocols and training for your team to help protect your company’s data and finances.
What is social engineering?
Broadly, a hack is any method of gaining unauthorized access to a computer or network. Social engineering refers to hacking strategies which exploit human error, and is sometimes called ‘human hacking.’
What’s the danger of social engineering to my business?
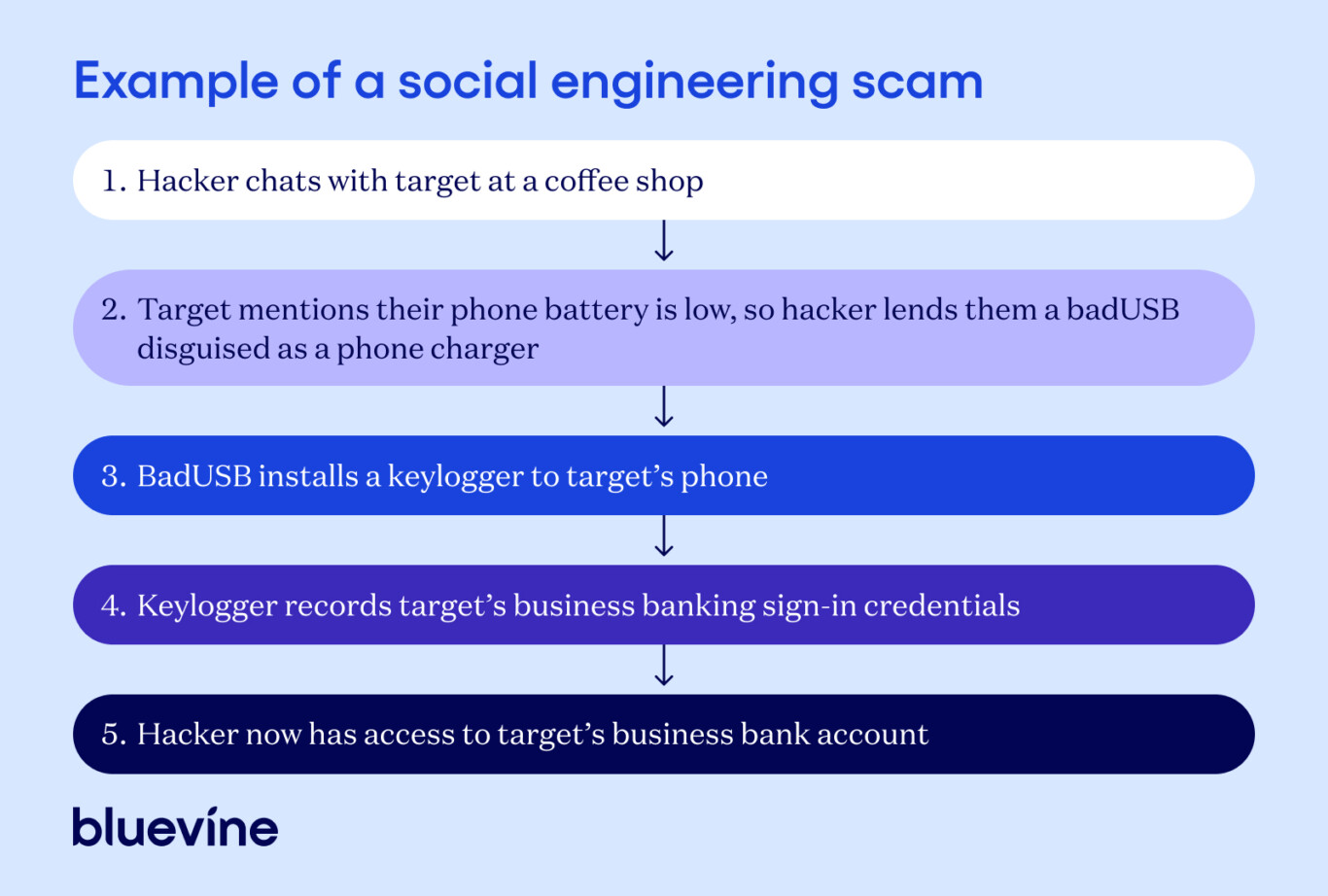
Large security breaches that cripple businesses often start with simple social engineering, as in the infographic below.
In the example above, steps 1 and 2 are simple social engineering, which clear the way for the hacker to commit account takeover fraud. To avoid this type of outcome, it’s important to understand social engineering strategies and take the necessary precautions to protect yourself.
The 3 basic principles of all social engineering scams
- The hacker impersonates a trustworthy or authoritative person or brand.
- The hacker exploits their target’s emotions with appeals to emotion, fear, or urgency.
- The hacker exploits their target’s good will or naivety.
How hackers use social engineering to steal employee information
There are a lot of social engineering strategies, but we can understand them intuitively by what type of security breach they are: psychological, digital, or physical. Some strategies may overlap categories, and many scams involve multiple strategies from different categories.
Psychological breaches
In which hackers create an asymmetric social balance, fooling their target into thinking they’re interacting with a trustworthy person or brand.
- Pretexting is creating a fake context to help extract sensitive information. Pretexting can be overt, like claiming to be a bank clerk and asking for sign-in credentials over the phone, or subtle, like expressing interest in working for you to learn where your employees park and eat.
- In catfishing or pig butchering scams, the pretext is an entire persona, developed over time based on the scammer’s interactions with the target.
- Baiting tempts targets to reveal personal information or download malicious code by offering something valuable, like money transfers or free media and software downloads.
- Phishing involves impersonating a trusted person or brand and using fraudulent emails, texts, social media messages, or phone calls to trick targets into revealing personal information or downloading malware.
Digital breaches
In which hackers use cyberhacking methods to trick targets into entering sensitive information on malicious sites or software.
- Trojan horses are methods of delivering malware by disguising them as benign links or files that, when opened, damage your computer’s code and/or steal your information.
- DNS attacks interfere with DNS infrastructure to redirect you to another site, inject malware into a site’s code, or intercept your session.
- When you visit a website, the Domain Name System (DNS) matches the site name to its IP address—it uses a name to find a location, like a phonebook.
- Watering hole attacks infect a website that’s frequented by a target group, rather than directly infecting an individual target. For example, a hacker might install a pop-up onto a KPI tracker or industry news website they know your employees use, then wait for just one employee to click it.
Physical breaches
In which hackers exploit social or operational protocols to physically acquire sensitive information or access.
- Tailgating is the act of following someone through a protected barrier—i.e., a door, turnstile, or gate that requires a badge scan, fingerprint, or password to access. Tailgating is often supported by pretexting, such as a hacker impersonating a delivery driver or maintenance worker.
- Dumpster diving is the simple act of stealing improperly disposed documents or other sensitive materials from bins or dumpsters. These can include visuals left over from a presentation, or sign-in credentials written on a sticky note.
Technologies that hackers can use
Theoretically, all a hacker needs to gain access to your business’s network is a computer (including simple computers like phones or graphing calculators), but other digital tools can assist them.
- BadUSBs are USB devices infected with malicious code, designed to be identical to ordinary devices like flash drives or charging cables. BadUSBs are an efficient way for hackers to install spyware.
- Facial recognition software has been enhanced by new AI tools, so hackers can find your entire online presence (including photos posted by other people or organizations) using small details of your face, such as your eyes.
- Keycard readers can clone nearby keycards or keycard apps running in your phone background, allowing hackers to digitally impersonate you to access your building.
- Keyloggers are a type of spyware that will store or send records of everything you type on a device. These can be installed via BadUSBs or—if your software is out-of-date—by hacking remote viewing software on employee devices.
- Large language models (LLMs) can impersonate the writing style of any author whose writing is fed to its machine learning algorithm, including yours.
How to protect your business from social engineering attacks
Hackers have a lot of tools at their disposal. Fortunately, it’s relatively straightforward to strengthen your business security against social engineers using three types of solutions: behavioral, operational, and technological.
As with the types of breach, these aren’t wholly distinct categories, as some of your strategies will overlap categories and you’ll use different strategies in conjunction with one another.
First, ensure you’re complying with the very basics of cybersecurity:
- Implement password security best practices
- Enable multi-factor authentication (MFA)
- Use industry standard third-party software for work
Behavioral solutions
In which you and your employees use natural and learned behaviors.
- Implement consistent training for you and your employees. Train all employees upon hiring and regularly thereafter, preferably once per year. Instill strong cybersecurity instincts that let employees identify scams early.
- Don’t leave devices unattended. Once you’ve signed into your phone or computer, don’t make it accessible to others. If you have to step away, either bring your device with you or sign out.
- Limit or privatize your social media presence. Make your personal information difficult to find by limiting what you share or setting your personal profiles to private.
Operational solutions
In which you and your employees stick to effective safety and security protocols.
- Manage employee access. Use accounts and tools which allow you to manage each employee’s level of access to sensitive materials, and grant employees their own sign-in credentials and MFA. Deactivate former employees’ access the day they’re terminated.
- Destroy sensitive or obsolete materials. Physically destroy sensitive documents and permanently delete sensitive data.
- Protect your employees’ information. As a business owner, you’re responsible for keeping your employees safe, so be judicious and always ask for consent before sharing their information or pictures on company social accounts—while this marketing strategy can humanize your business, it can also make employees vulnerable to hacks.
Technological solutions
In which you and your employees bolster your cybersecurity in simple but effective ways.
- Keep your WiFi network private. Whether you’re working from an office building or a home office, keep your networks password protected.
- Avoid public networks, even encrypted ones. WiFi at coffee shops, hotels, and airports can be hacked to steal information from connected devices.
- Encrypt your files and use VPNs. To encrypt a file is to scramble it in a specific way, making it impossible to read without a key. Use your operating system’s tools to encrypt files, and use a Virtual Private Network (VPN) to encrypt sessions with other sites or servers.
- Keep your operating system’s security features on and up-to-date. Cybersecurity programs like firewalls and antivirus software can help protect you, but the easiest and most effective thing you can do is keep your device operating systems up-to-date.
How to respond to a social engineering attack
If you’ve been targeted for financial fraud, take the following steps:
- Block any communication channels with scammers or compromised accounts.
- Disconnect your device from the internet to prevent the spread of malware, but keep the device on so you can collect evidence, if needed.
- Call your banking provider and freeze your account—don’t pay any ransoms or other sums to the hacker.
- Contact your local police department and report the incident to the FBI’s Internet Crime Complaint Center.
- Change your passwords.
How you can recover your device or accounts will depend on the nature of the attack. Collaborate with an IT specialist (internal or outsourced) to determine your next steps.
See all the ways Bluevine helps keep your account secure.